At Opticon 2022, I was able to get a sneak preview of what was known as the “Product Switcher.” As a contractor, we do new implementations, as well as ongoing development updates, for numerous clients at one time. Instead of having to have an endless rolodex of bookmarks full of client environment login URLS, there is a SINGLE login interface that will allow for seamless switching between client environments. This was later to be renamed to OptiID.
DISCLAIMER: AS OF TODAY, JUNE 17 2023, THIS IS A BETA PRODUCT. THE FOLLOWING FUNCTIONALITY MAY NOT REFLECT THE FINAL PRODUCT. THIS IS SIMPLY MY EXPERIENCE WITH THE ONBOARDING AND MY FIRST-THOUGHTS ABOUT THIS PRODUCT.
In my opinion, this was the single best piece product that was(nt) announced at Opticon.
After bugging almost everyone on the product team every so often (Sorry John + Anders), I was allowed the opportunity to join the beta.

Onboarding
As an early adopter, onboarding was still absolutely painful. WHICH IS FINE!
This process was heavily relying on so many different departments and teams, specifically a huge change in how the product vs organization vs permissions interacted together.
As an OMVP, we do get access to sandboxes, BUT they are related to the organization that we are currently working for. This posed my first problem, which was that one of my sandboxes was technically still linked to a previous employer.
Once that was shuffled around, the next problem arose….SSO!

I do have my own Azure AD instance, but, to be honest, I literally have never used it for anything like this. The early documentation didn’t have a TON of helpful information, so it was really just a shot in the dark.
Lastly, Some of the problem also was that there was a lot of confusion between the leadership in my company, who also wanted to join this beta, and myself as an OMVP. Papers got shuffled enough that my company actually was never able to participate in the beta.
In the end, I chalk this up to the different team members learning how to implement this, especially on a global scale. I firmly believe that my case was a corner case, so I do not fault the team in any way. They were always amazing at getting back to me with any concerns.

Implementation
Once into the system, the implementation into the products was really still just a stab in the dark for what will and wont work.
The only real “self-configurable” product that is available at this moment in time is the CMS. (Configured Commerce is on the way)
In order to make it work, they provided a prerelease offline nuget package of the new OptimizelyIdentidy package and Episerver.UI package.
Once those are installed, all you’ll have to do is remove the CmsAdmins and CmsEditors from the application.json, and add this line of code into the startup.cs
services.AddOptimizelyIdentity(useAsDefault: true);
While that did end up working, in a way, the documentation does not tell you that you need to apply a product (and permissions for that product) to a role, and then implement that role into a group, and then apply users to that group.
Just to reiterate how this works:
- Roles are the named permission levels for the products
- Roles have out of the box values, but can also be manually created
- Manually created groups are assigned to a specific product + environment (example, CMS is the product, and Integration is the environment)
- Groups can contain one or more role
- Groups can also contain one or more product (products here are broken out by the product name and then environment)
- Groups can contain users
- When users are assigned to that group, they are given the defined roles to the defined environments
It sounds like a lot, but it does make sense!

First Thoughts
This week (week of Jun 12th) was my first week in the system, and the very first thing I noticed was pretty huge…and I’m not sure if it is announced. If not…..SURPRISE??
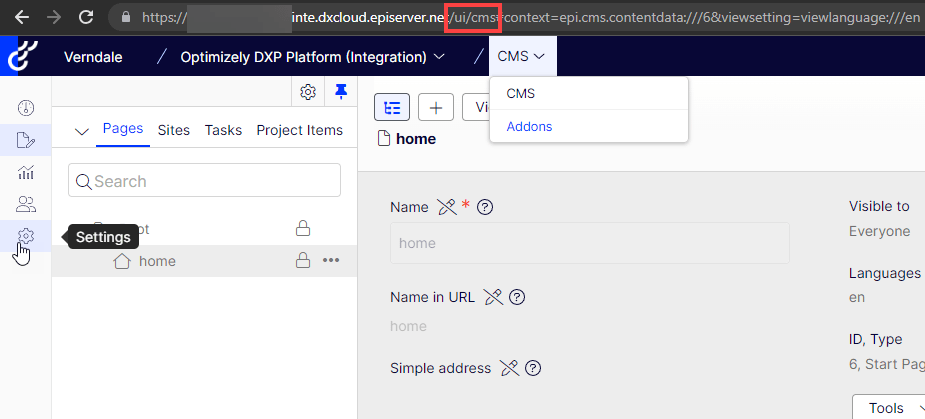
The CMS login URL suddenly returned a 404. Let’s take a moment of silence for “/episerver/cms”.
The new login URL is going to be “/ui/cms”, which will take you directly to the SSO login page, and then redirect you right back after you’re authenticated.
This also comes with a brand new side-nav, which is very different, but pretty neat!
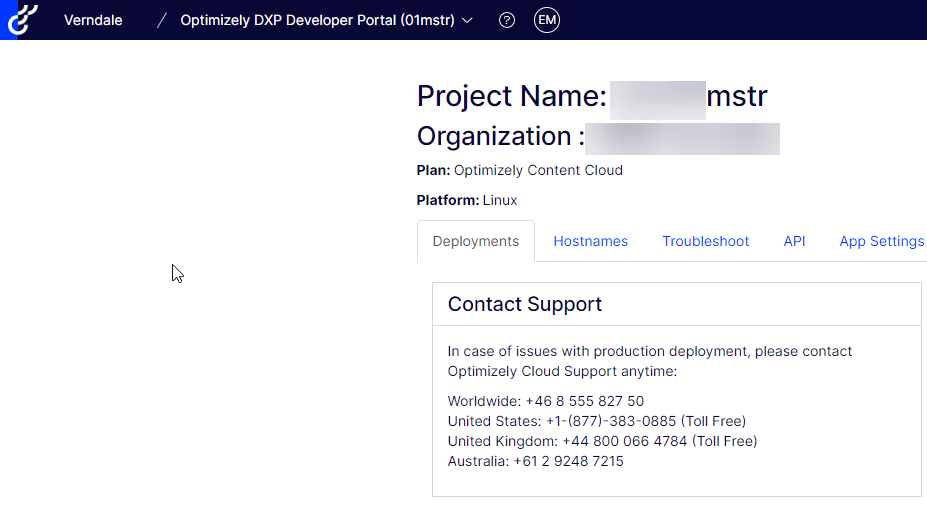
Other than the CMS, being that this isn’t completely set in stone, there really isn’t much else different in the products. It is really cool that I am able to get to almost every product without searching for links.
Currently, the only products that have not been able to tested, due to the teams not having the functionality ready, is Configured Commerce and Content Recommendations
I am honestly waiting to see what the other features are going to be closer to launch.
The things I’m looking for are the following:
- How to deal with non-SSO users in CMS (Local Accounts)
- At the time of writing this, this functionality has not been pushed to the beta, but does exist and will be released
- Learning how a Technical Implementation Partner can co-exist in a client-environment
- Specifically to be able to allow clients to manage users during and/or after go-live
- What is the onboarding process for new clients? What about for partners?
- Is this going to be granted with the PAAS Portal access?

Conclusion
Honestly, I’m over the moon about this product.
Over the past few years, Optimizely has acquired a lot of products, and the pathway for them to all be integrated together has been pretty cloudy until…NOW!
It suddenly feels like one big cohesive set of products.
I am confident in the onboarding team that the issues will be worked out. This is too important of a product for the long-term usability of these products.
GA for this product, as of writing this, should be at the end of June. Keep an eye on the Optimizely blog for more information!
Resources
- Opti ID Documentation: https://support.optimizely.com/hc/en-us/sections/12612322579597-Opti-ID
- Optimizely Blogs: https://world.optimizely.com/blogs/
